
Map your evolving
attack surface
Automatically discover and map your exposed assets to gain continuous, real-time visibility into your entire digital footprint. Always know exactly what needs to be protected before attackers find it.


Offensive Security &
Exposure Management Platform



Automatically discover and map your exposed assets to gain continuous, real-time visibility into your entire digital footprint. Always know exactly what needs to be protected before attackers find it.

Go beyond traditional, point-in-time assessments. Combine continuous vulnerability discovery with elite, crowdsourced human ingenuity for comprehensive security that scales as you grow.

Transform fragmented vulnerability data into a unified, centralised reporting that supports internal security, governance policies and alignment with SOC2, ISO 27001, DORA, NIS2, and more.
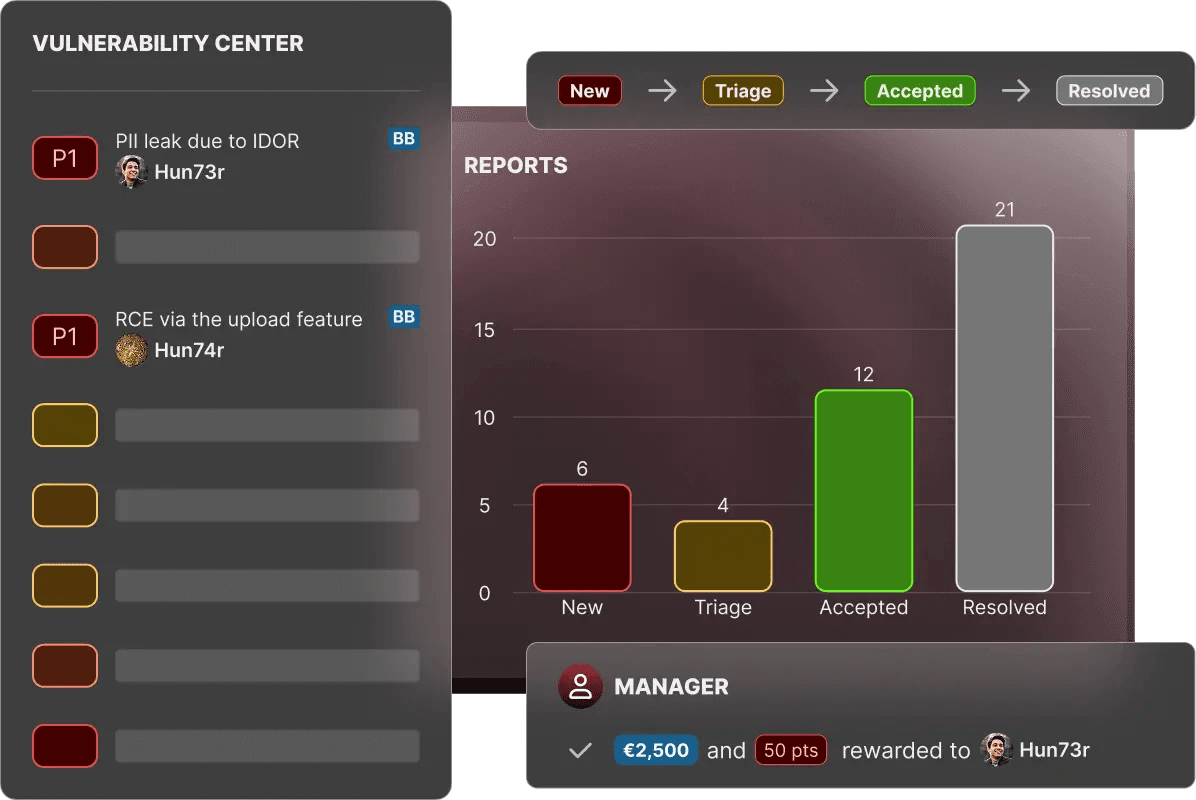
Leverage the skillsets of tens of thousands of fully vetted ethical hackers – experts at finding critical vulnerabilities in your online assets. Benefit from a crowdsourced, platform-driven and pay-for-results approach to security testing and align vulnerability assessment to your security, IT and business requirements.










"Our partnership with YesWeHack has been smooth, professional, and incredibly valuable. We backed the right horse and have never regretted our decision!"

"Adopting a crowdsourced model has helped us identify previously overlooked vulnerabilities and has become a valuable component of our overall security strategy."

"YesWeHack is a key component of L’Oréal’s cybersecurity strategy, bridging the gap between security-by-design and continuous monitoring to ensure the highest level of protection for our assets and the PII of our consumers, customers, and employees."

"Our partnership with YesWeHack has been smooth, professional, and incredibly valuable. We backed the right horse and have never regretted our decision!"

Harness the power of crowdsourced security to supercharge the discovery and remediation of vulnerabilities.
