
Get continuous visibility
of your digital footprint
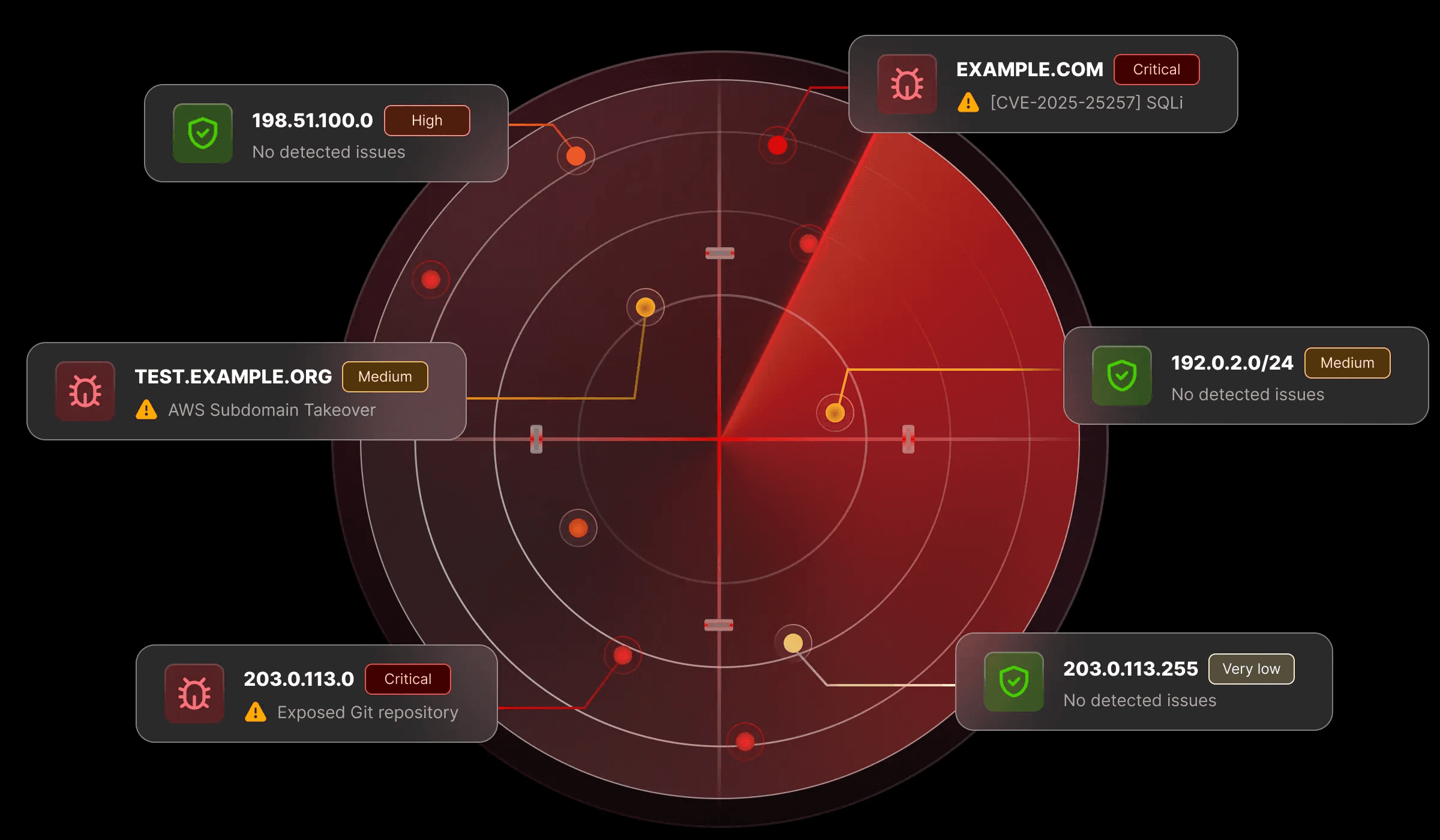
Get a comprehensive view of your internet-facing assets such as web applications, APIs and cloud infrastructure.


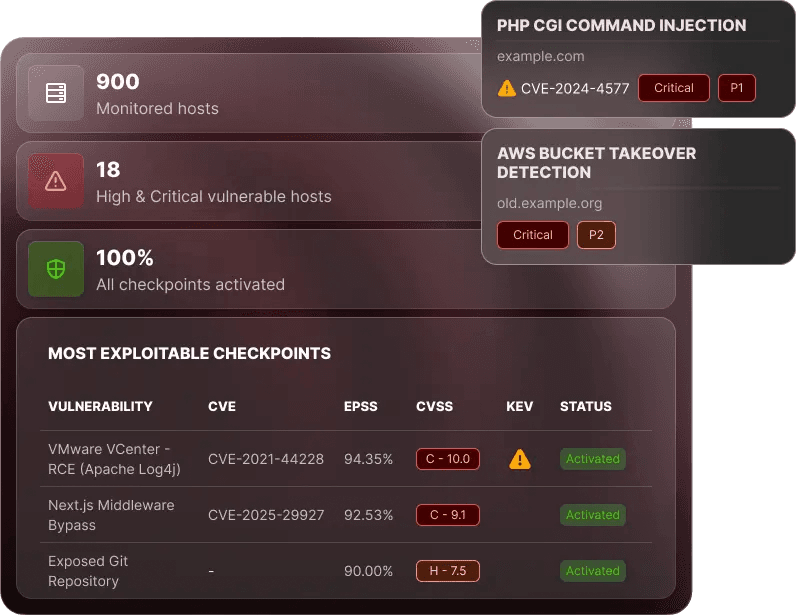
Constantly assess your entire attack surface against vulnerabilities actively exploited in the wild, without overwhelming your assets or your team.
Digital transformation drives the expansion of attack surfaces, while new vulnerabilities emerge constantly. As a result, organisations struggle to maintain a clear and accurate view of risk. Without ongoing visibility and assessment, they're always steps behind the threats that matter.
Autonomous Pentest provides a comprehensive view of all organisations' assets combined with targeted checkpoints that continuously assess the entire attack surface against the most exploited vulnerabilities.


Get a comprehensive view of your internet-facing assets such as web applications, APIs and cloud infrastructure.

Identify vulnerabilities that matter most: trending CVEs, misconfigurations and subdomain takeovers. Stay ahead of mass exploitation campaigns with our curated checkpoints.

Stop drowning in vulnerability alerts. Cut through the noise with high-value findings and automatically prioritised risks.









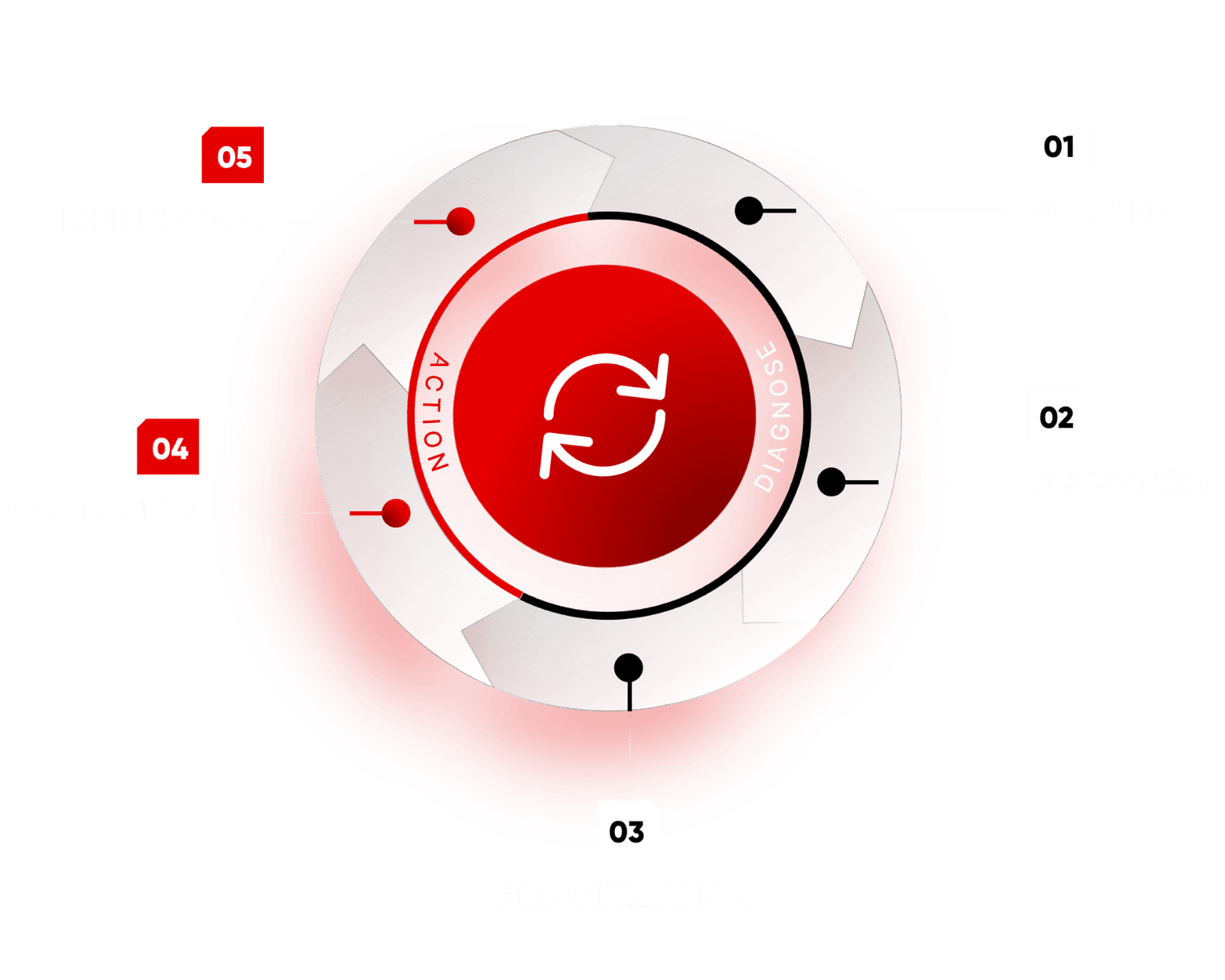
Continuous Threat Exposure Management (CTEM) is the ongoing process of discovering, assessing, and addressing risks across all your exposed assets. Unlike periodic point-in-time assessments, CTEM delivers continuous visibility of your evolving attack surface and emerging vulnerabilities as they appear.
The framework operates through five integrated phases:
YesWeHack's Autonomous Pentest solution unifies all five phases in a single platform.








Get continuous visibility and targeted checkpoints that detect the threats driving today’s breaches, without overwhelming your team.
